The correct answer is C. The session is offloaded using NPU .
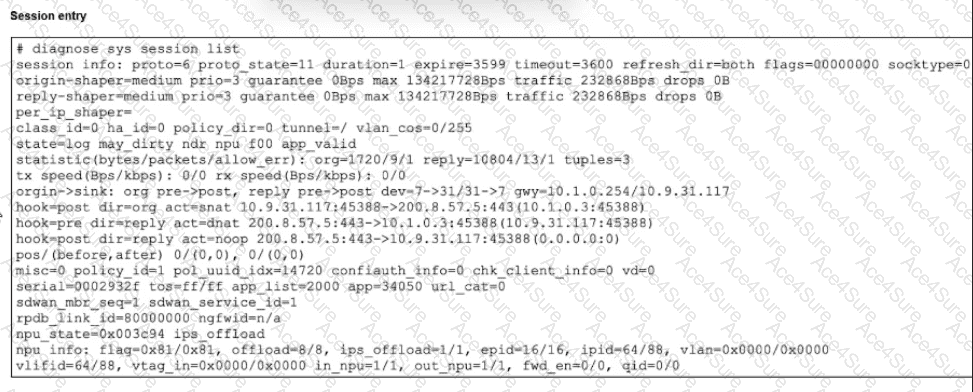
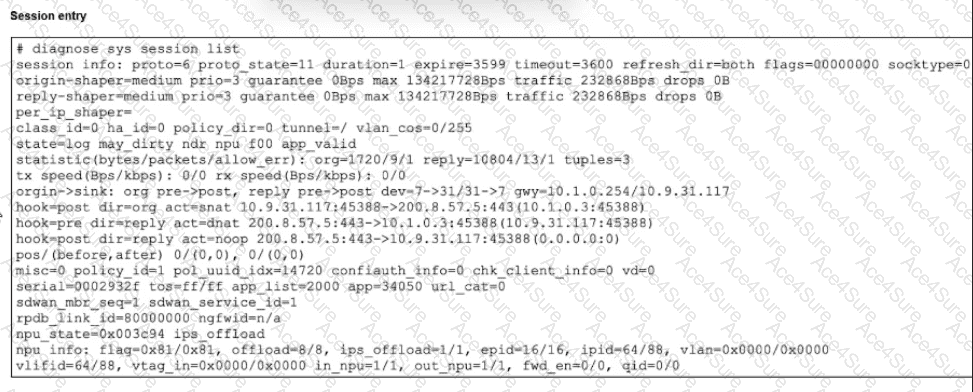
The exact session example in the study guide shows:
proto=6 → this is a TCP session
expire=3599 → the session will expire in 3599 seconds , not in one second
hook=post dir=org act=snat 10.9.31.117:45388- > 200.8.57.5:443(10.1.0.3:45388)
hook=pre dir=reply act=dnat 200.8.57.5:443- > 10.1.0.3:45388(10.9.31.117:45388)
npu info: ... offload=8/8 ...
and the slide explicitly states: “Offloaded in both directions using NP6”
The study guide also explains this exact point clearly:
“Counters for hardware acceleration—The presence of the npu info field indicates the session has been offloaded to hardware acceleration. In this example, traffic is being offloaded in both directions using network processor (NP) 6, which is represented by the value of 8.”
Why the other options are wrong:
A is wrong because expire=3599, not 1. The duration=1 field means the session has existed for 1 second, not that it will expire in 1 second.
B is wrong because the original session is from 10.9.31.117 to the remote server 200.8.57.5:443. The IP 10.1.0.3 is the SNAT-translated source address , not the final destination.
D is not the best answer for this single-select question . The reply is indeed DNATed back toward the original client, but the exact validated takeaway highlighted by the study guide for this exhibit is the NPU offload state .