“You may need to exempt traffic from SSL inspection if it is causing problems with traffic, or for legal reasons.”
“Performing SSL inspection on a site that is enabled with HTTP Strict Transport Security (HSTS), for example, can cause problems with traffic. Remember, the only way for FortiGate to inspect encrypted traffic is to intercept the certificate coming from the server and generate a temporary one. After FortiGate presents the temporary SSL certificate, browsers that use HSTS refuse to proceed.”
“Laws protecting privacy might be another reason to bypass SSL inspection. For example, in some countries, it is illegal to inspect SSL bank-related traffic. Configuring an exemption for sites is simpler than setting up firewall policies for each individual bank. You can exempt sites based on their web category, such as Finance and Banking...”
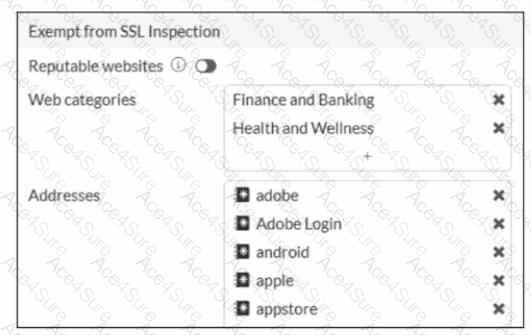
“The predefined deep-inspection and custom-deep-inspection profiles exclude some web categories—Finance and Banking, and Health and Wellness—and some FQDN addresses...”
Technical Deep Dive:
The correct answers are B and D .
B is correct because the study guide explicitly says SSL inspection may be bypassed for legal reasons , especially where privacy laws restrict inspection of sensitive categories such as Finance and Banking . The same privacy rationale also explains why Health and Wellness is commonly exempted.
D is correct because some sites break under deep inspection due to HSTS . FortiGate must generate and present a temporary certificate during full SSL inspection, and browsers enforcing HSTS can reject that interception flow. That is why some sites are exempted from deep inspection.
Why the others are wrong:
A is not stated in the guide.
C refers to the separate Reputable websites option, which is a FortiGuard-maintained allowlist feature, not the reason the predefined categories shown in the exhibit are excluded.
From an operational standpoint, this is a classic balance between security visibility and application/legal compatibility . Deep inspection gives FortiGate payload visibility, but it can interfere with pinned-certificate/HSTS behavior and can violate privacy policy for regulated content.