Amazon Web Services SCS-C02 Question Answer
A company wants to establish separate IAM Key Management Service (IAM KMS) keys to use for different IAM services. The company'ssecurityengineer created the following key policy lo allow the infrastructure deployment team to create encrypted Amazon Elastic Block Store (Amazon EBS) volumes by assuming the InfrastructureDeployment IAM role:
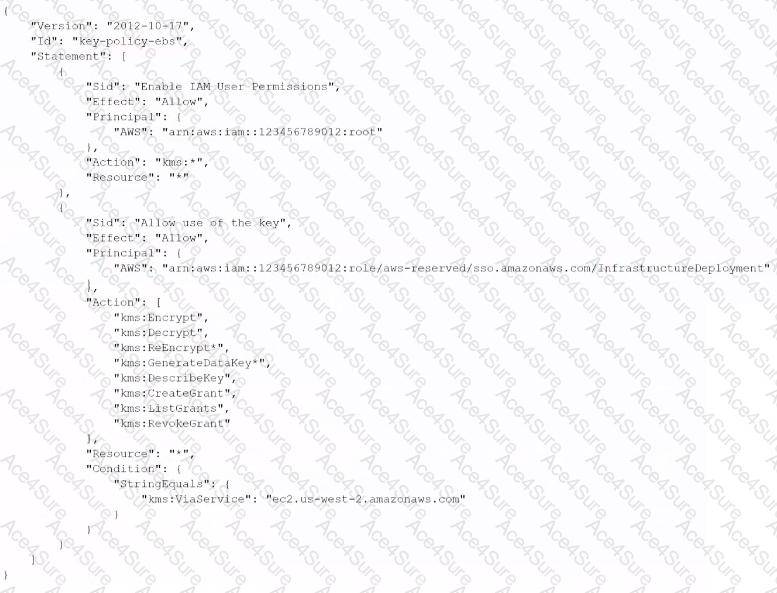
The security engineer recently discovered that IAM roles other than the InfrastructureDeployment role used this key (or other services. Which change to the policy should the security engineer make to resolve these issues?


