CompTIA PT0-003 Question Answer
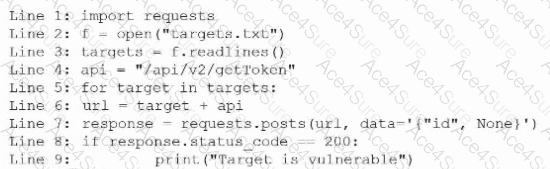
During an engagement, a penetration tester receives a list of target systems and wants to enumerate them for possible vulnerabilities. The tester finds the following script on the internet:
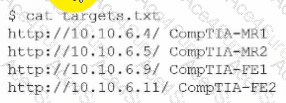
After running the script, the tester runs the following command:
Which of the following should the tester do next?


