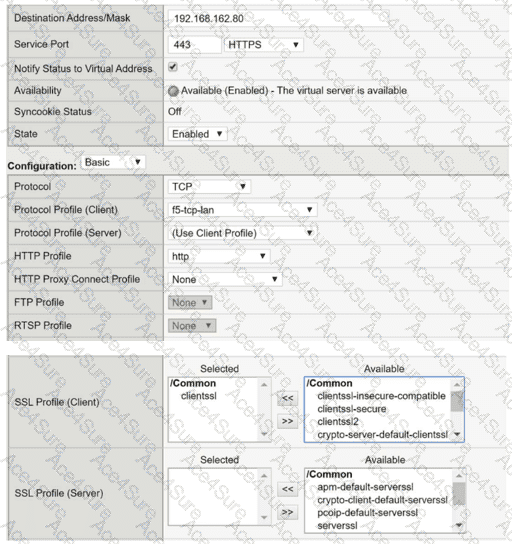
To successfully performSSL offload and re-encryptionon a BIG-IP system, the virtual server must be configured withboth a Client SSL profile and a Server SSL profile. The Client SSL profile enables BIG-IP to decrypt inbound HTTPS traffic from clients, while the Server SSL profile is required tore-encrypt traffic before forwarding it to the pool members.
From the exhibit, the virtual server has aClient SSL profile configured, which allows BIG-IP to accept HTTPS connections from clients. However, there isno Server SSL profile attached, meaning BIG-IP attempts to sendunencrypted HTTP trafficto pool members listening on HTTPS (port 443). This protocol mismatch causes the server-side SSL handshake to fail, resulting in users being unable to connect to the application.
This behavior is well documented in BIG-IP SSL troubleshooting guides: when backend servers expect HTTPS, a Server SSL profile is mandatory to establish a secure connection from BIG-IP to the pool members.
The other options are incorrect:
Removing the Client SSL profile (Option A) would break client-side HTTPS.
The server-side TCP profile (Option B) is unrelated to SSL encryption.
Forward Proxy (Option C) is only used for outbound SSL inspection scenarios.
Therefore, configuring anSSL Profile (Server)is the correct and required solution.