Cisco 350-701 Question Answer
Refer to the exhibit.
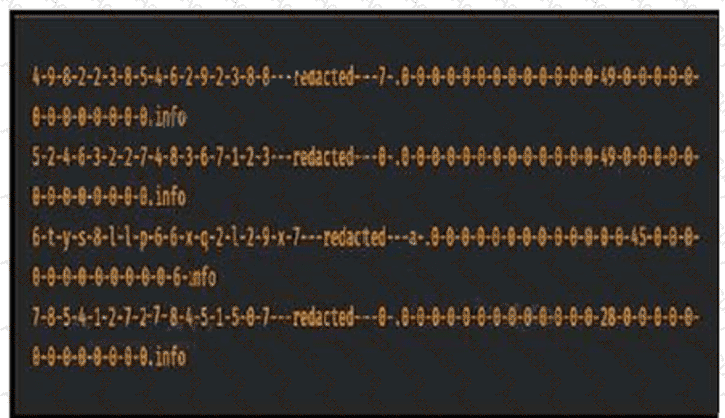
Consider that any feature of DNS requests, such as the length off the domain name
and the number of subdomains, can be used to construct models of expected behavior to which
observed values can be compared. Which type of malicious attack are these values associated with?


