Cisco 300-215 Question Answer
Refer to the exhibit.
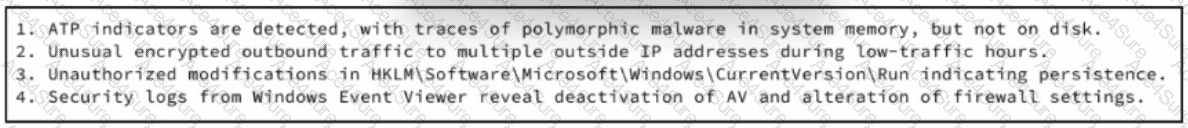
An experienced cybersecurity analyst is investigating a sophisticated suspected breach on a Windows server within an enterprise network and compiled the evidence gathered so far Which action should the analyst prioritize to understand the scope and impact of the breach?


